Xbox’s consoles do not sell well but generate good revenue
Last year the deal that many Xbox players were waiting for finally closed, it was the acquisition Activision BlizzardSpending, which...
The failure of the Vision Pro led to lower Apple production
A couple of months ago, Apple took a new leap in technology, from 2012 Vision ProAugmented reality viewer that gives...
They shared data from the first NES Zelda prototype
Thanks to the power of the Internet, a lot of information has been released from the world of video games,...
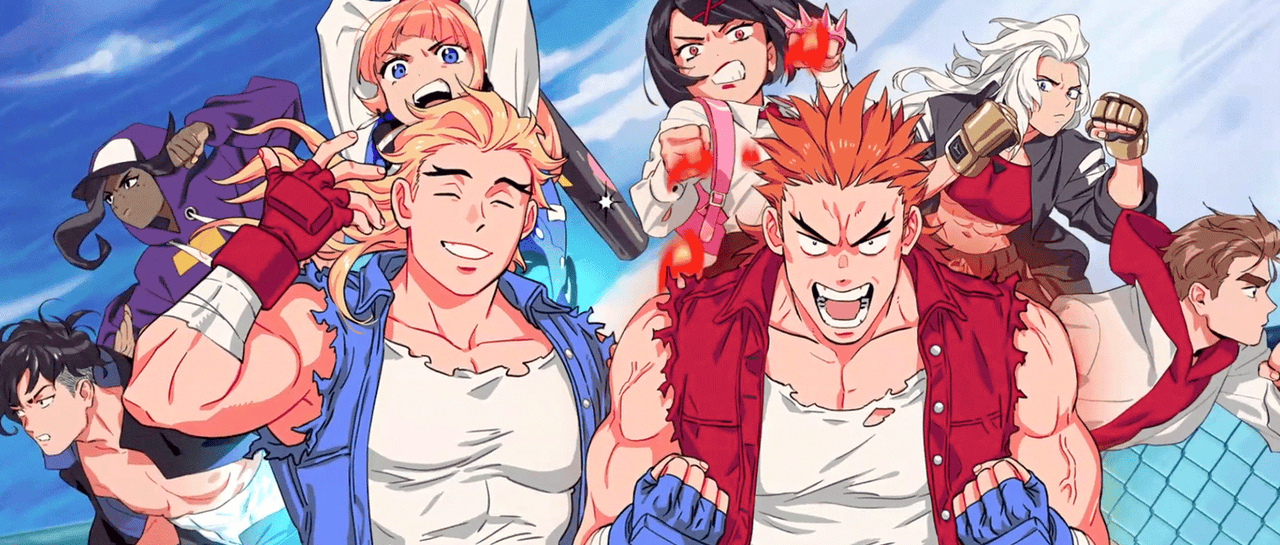
Check out the DLC D Double Dragon for River City Girls 2
It's been almost two years since one of the world's most beloved arcade games was released. way aheadwe talk River...
Nintendo forced to remove years of content from Gary’s Mod
A title that has been around for several years for those who don't have it on their radar Garry's MODon...
The Bluey series would have become the new Lost
For years now, a Disney series has managed to place itself in the hearts of fans and that's it bluey,...
Suicide Squad still fails Atomics
It is a fact that Suicide Squad: Kill the Justice League The biggest flop of 2024. After 10 years of...
GTA Online has been updated with double rewards
This last year's popularity GTA Online has increased, precisely because users are eagerly awaiting the arrival of the next important...