You can take a picture with Pikachu in Mexico
The world of Pokémon was previously far from Latin America, as collectible cards, games, merchandise, and more were brought in...
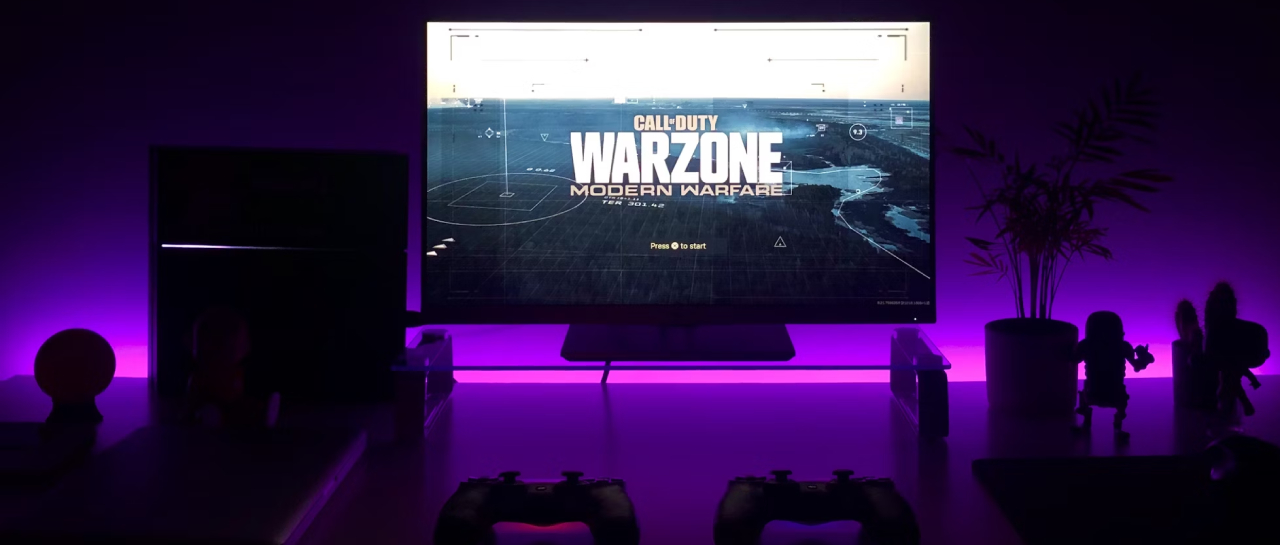
VPN to play Warzone: Maximize your performance and security
when you play Call of Duty: Warzone, one of the most frustrating experiences is dealing with latency and geo-restrictions. Here...
Microsoft Xbox has taken over the PlayStation Store from Sony 🤯
What you need to know Microsoft Gaming is a new entity within Microsoft which includes Bethesda, Activision-Blizzard and Xbox. As...
Kingdom Come Deliverance 2 is a reality! | Atomics
It was launched in 2018 Kingdom liberation comes, the first title from Warhorse Studios, an independent studio from the Czech...
WhatsApp will make a controversial change Atomics
Meta is constantly working to improve the experience WhatsApp. While some of the implemented changes are well received, others are...
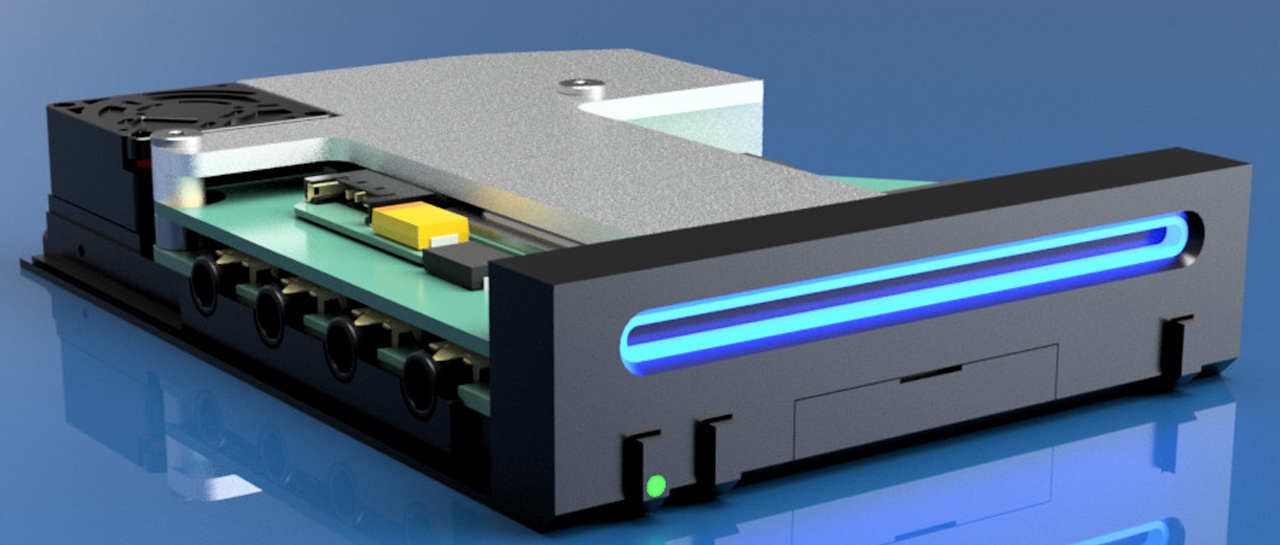
The Wii Mini is a reality, and it works Atomics
After the success of the NES and SNES Mini, many would think that Nintendo would offer smaller versions of its...
Samsung makes new hardware for Pixel 9 official
A few days ago, insiders announced that Google will also use the new Samsung hardware for the Pixel 9. What...
Nothing integrates ChatGPT into its in-ear headphones and NothingOS
Nothing just announced that it's going to integrate ChatGPT into its smartphone operating system, Nothing OS, and software for all...