The new Google Pixel 8a and the latest leaks
In about a month, Google will release its next new Android phone, and in the meantime, the dams are slowly...
A new gender-swapped ninja is likely to be released as Mortal Kombat 1 DLC
Mortal Kombat 1 got its latest downloadable character on Ermack today, but it looks like we may now know...
AirPods Pro 2 Hacks: Secret Features to Boost Your Sound
Apple's AirPods Pro 2 are still some of the best wireless earbuds on the market, a year and a half...
Televisa plans to merge Izzy with Sky
It is well known that cable and Internet services in Mexico have been in constant competition for many years Cablevision...
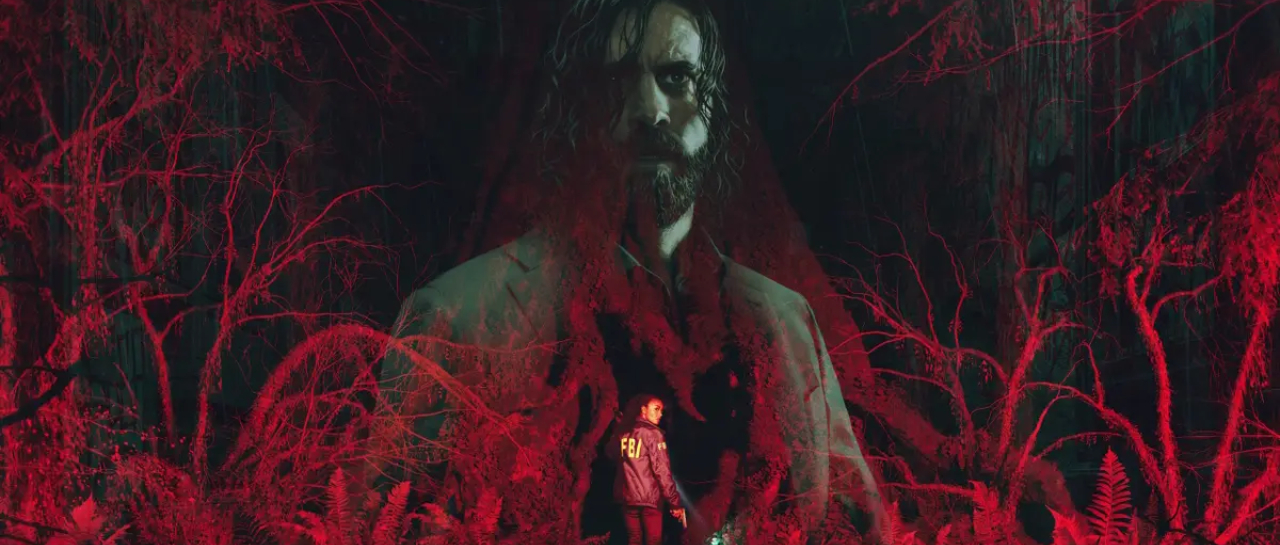
They used bots to boost sales of Alan Wake 2
A lot of great games were released last year, including ours Alan Wake 2A continuation of the story as originally...
More Dragon Ball: Sparkling characters revealed! zero
Its voting rights dragon ball This year relevance will return with its video games Sparking! zeroWhich is the goal of...
NES Emulator has arrived on the iPhone Store
As is well known, the rules of applications in the Apple environment have changed a bit, since they finally got...
Many layoffs have been confirmed at Take Two Interactive
This year has been complicated in the video game industry, as only the first few reported that some major companies...